Cryptography: or the History, Principles, and Practice of Cipher-Writing (1898)
Frederick Edward Hulme (1841–1909) was an artist, naturalist and antiquarian who loved to write books. He did so on flowers, butterflies, moths, Christian art, heraldry, flags, proverbs, and folklore. In 1898 he bent his pen towards Cryptography, an exploration of covert communication through history. “That which is secret and mysterious,” he wrote, “calling for acute intelligence to penetrate its meaning, has always exercised a great fascination on the human mind.” And none more so than Hulme’s. The book is full of enthusiastic attempts to find the value in ancient cipher systems, though these often come to nothing: “One finds over and over again things commended by various writers that entirely break down when brought to the vital test of actual experiment.”
Like all good cryptanalysts (and historians) Hulme stands at an acutely critical angle to his subject. He puts to the sword a number of seemingly valuable techniques, such as inventing special characters: “If we recognise that a certain form is the symbol of a certain letter, we soon learn to recognise this form when we see it, and its shape is a matter that is absolutely indifferent to us.” He shows us that simple substitution ciphers can be cracked with a bit of patient analysis. The commonest letter in an encrypted message, for example, is very probably “e” in disguise.
Hulme gives short shrift to the substitution cipher created by Elizabethan polymath Francis Bacon (1561–1626), which replaces each letter of the alphabet with five others. He condemns it both for how easy it is to decipher and how long it takes to use. In Bacon’s cipher, the word “cryptogram” resembles a baby's babble:
AAABABAAAABABBAABBBABAABAABBABAABBABAAAAAAAAAABABB
Nevertheless, Hulme praises Bacon’s three essential principles of a good cipher: facility in execution; difficulty in solution; and clearness from suspicion. (He doesn’t bother himself with the Baconian theory of Shakespeare authorship, which was then at its apogee, after the recent publication of Sir Francis Bacon's Cipher Story (1893–95) by Orville Ward Owen.)
Though they aren’t strictly ciphers, Hulme does have a lot of time for "concealing text". He finds that letters written with the juice of oranges and onions “or almost any sharp things” can be made to appear by the warmth of a fire as if by magic. And letters of vinegar become visible by gently rubbing soot into them. The strangest mode of concealment is also the slowest: “One plan gravely commended was to shave a slave’s head, and then to write upon it any message one might wish to send. When the hair was sufficiently grown to conceal the matter, the man was dispatched to the person with whom it was desired to communicate, and he in turn shaved the victim and read off the message.”
The Greek slave in this story is not the only person who has suffered in the interests of covert communication. Johannes Trithemius (1462–1516), the Benedictine monk who wrote the first really elaborate treatise on cryptography, “was accused of dabbling in the black art and holding converse with demons. He was therefore brought to trial for these magical incantations, and had a very narrow escape of being burnt.” Another early modern figure was not so fortunate: “The correspondence of King Charles was captured by the Roundheads at Naseby—a correspondence which Dr. John Wallis, a distinguished mathematician of those days, analysed and finally deciphered, and which ultimately cost the defeated monarch his head.”
The last pages of the book consider various modern ciphers: The grill; revolving grill; slip-card; Mirabeau; Newark; clock-hands; two-word. Hulme was worried that some of his Victorian readers would condemn his book as a facilitator of wrongdoing. Thus at the outset he contends that any powerful science may be co-opted for wicked ends: “From the researches of chemistry may be derived . . . the healing medicine . . . or the subtle potion of the secret poisoner.” And the last line of the book completes his apology. In time of peril, Hulme argues, a knowledge of cryptology “may save hundreds of lives, or avert catastrophe from the nation itself.” If he had lived long enough to know of Alan Turing and the cryptanalysts at Bletchley Park, he could have upped that figure to millions.
Enjoyed this piece? We need your help to keep publishing.
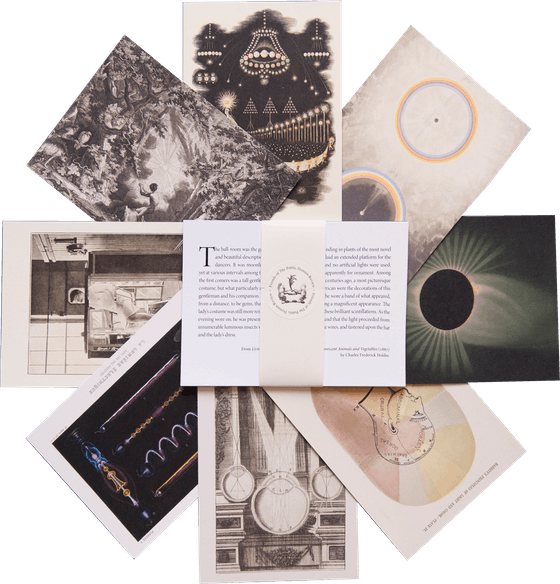
The PDR is a non-profit project kept alive by reader donations – no ads, no paywalls, just the generosity of our community. It’s a really exciting model, but we need your help to keep it thriving. Visit our support page to become a Friend and receive our themed postcard packs. Or give a one-off donation. Already a supporter? A huge thank you for making all this possible.
Feb 14, 2018